Indian Prime Minister Narendra Modi's Bharatiya Janata Party (BJP)-led alliance raced to a clear majority in early vote-counting.
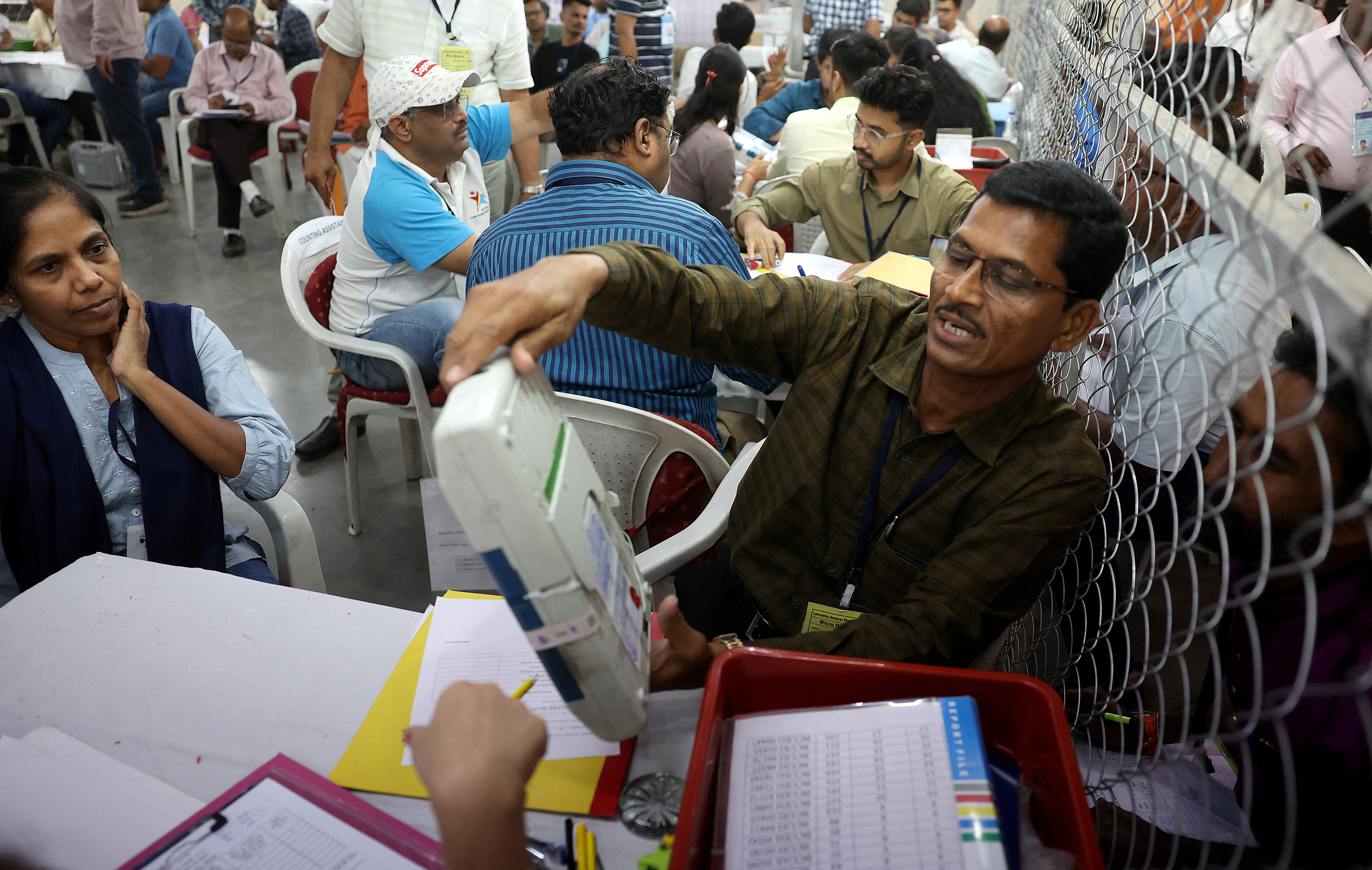
Election staff members count votes inside a vote counting centre in Ahmedabad, India, June 4, 2024. REUTERS/Amit Dave - World
Indian Prime Minister Narendra Modi's Bharatiya Janata Party (BJP)-led alliance raced to a clear majority in the 543-member lower house of parliament in early vote-counting trends on Tuesday, TV channels showed.
Tiananmen Square Anniversary
Security was tight and access restricted to Beijing's Tiananmen Square on Tuesday, the 35th anniversary of the June 4 crackdown, while Hong Kong also increased policing as activists in Taiwan and elsewhere prepared to mark the date with vigils.
Police stand guard at Causeway Bay, ahead of the 35th anniversary of the crackdown on pro-democracy demonstrators at Beijing's Tiananmen Square in 1989, near where the candlelight vigil is usually held, in Hong Kong, China, June 3, 2024. REUTERS/Tyrone Siu/File Photo
Markets
Talking Points
The U.S. said on Monday it wants the United Nations Security Council to adopt a resolution backing the proposal outlined by President Joe Biden to end fighting between Israel and Palestinian militants Hamas in the Gaza Strip.
Smoke and flames rise during an Israeli air strike in central Gaza Strip, June 3, 2024. REUTERS/Ramadan Abed
The Proud Boys are back. Four years after the failed effort to overturn Trump’s 2020 electoral defeat, the violent all-male extremist group that led the storming of Congress on Jan. 6, 2021, is rebuilding and regaining strength.
[1/4]A member of the far-right Proud Boys stands for a portrait before a campaign rally for former U.S. president and Republican presidential candidate Donald Trump in Wildwood, New Jersey, May 11, 2024. REUTERS/Jim Urquhart
As the local climate has heated up over decades, rivers and lakes have also shrunk.
Defending champion Novak Djokovic produced a superhuman effort to subdue Argentine Francisco Cerundolo 6-1 5-7 3-6 7-5 6-3 on Monday and reach the quarter-finals of the French Open, as the top seed shrugged off a knee issue for a milestone win.
Tennis - French Open - Roland Garros, Paris, France - June 3, 2024 Serbia's Novak Djokovic reacts after falling during his fourth round match against Argentina's Francisco Cerundolo REUTERS/Yves Herman
Mexico Election
Claudia Sheinbaum basked in the glow of a thumping presidential win late Sunday, thanking supporters who gathered at the capital's iconic Zocalo plaza shortly after 1 a.m. to applaud Mexico's first female president.
Presidential candidate of the ruling Morena party Claudia Sheinbaum, reacts while addressing her supporters after winning the presidential election, at Zocalo Square in Mexico City, Mexico June 3. REUTERS/Alexandre Meneghini
Hunter Biden Trial
A jury was sworn in on Monday for the trial of Hunter Biden on gun charges, a historic criminal prosecution of a sitting president's son with the potential to influence the 2024 presidential election.
Hunter Biden, son of U.S. President Joe Biden, departs the federal court with his wife Melissa Cohen Biden, on the opening day of his trial on criminal gun charges in Wilmington, Delaware, U.S., June 3, 2024. REUTERS/Kevin Lamarque - Legal
Hunter Biden, the son of U.S. President Joe Biden, is scheduled to go on trial on June 3 in Delaware on charges he violated federal gun laws in 2018 when he purchased a firearm.